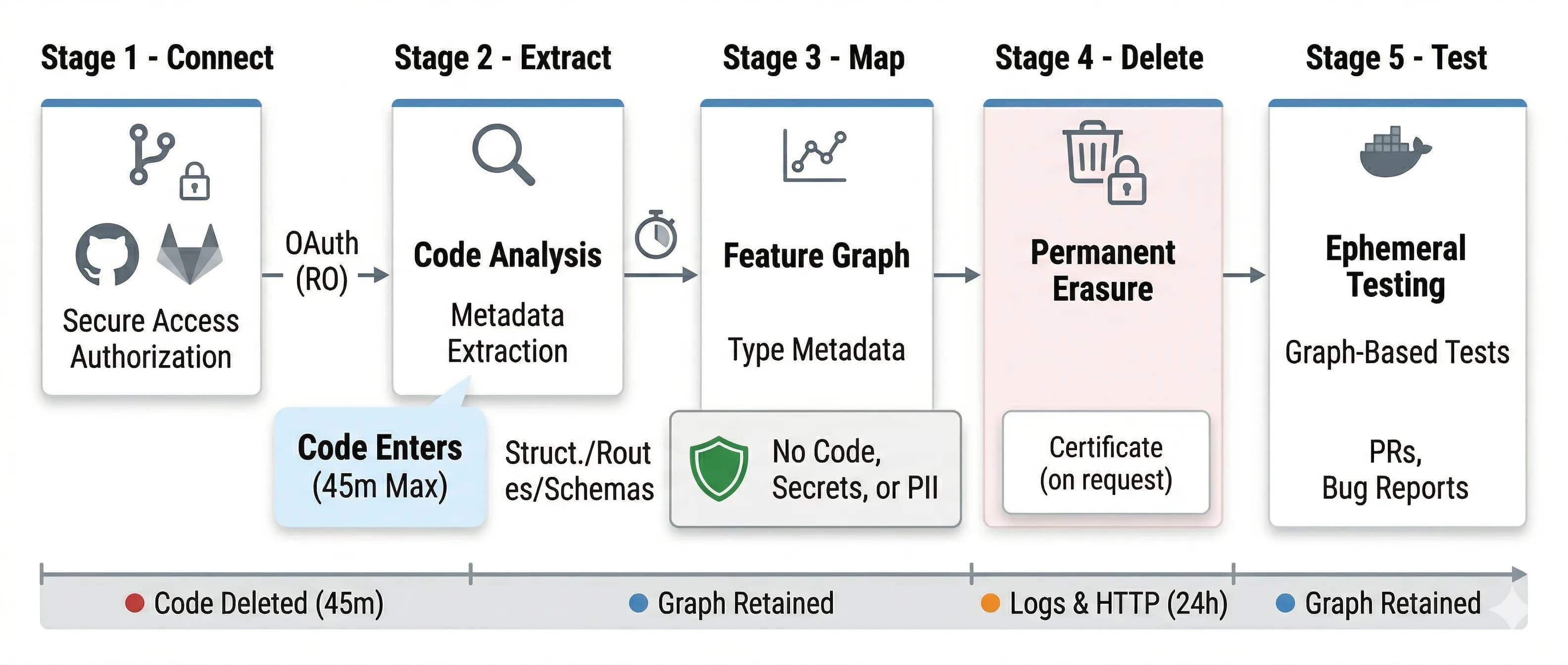
We delete your code after reading it.
Read-only OAuth. Source deleted in 45 minutes. Customer-scoped encryption keys. Here’s exactly what we do with your data.
Source code lifecycle
Cloned once, analyzed, then source code deleted. Maximum 45 minutes. Most deletion completes within 30.
OAuth permissions
We do not
- Train models on your code
- Use your code in benchmarks or examples
- Share code with any third party
- Retain code for debugging — we log the error, not the code
- Keep code in backups
Need to verify deletion? Email security@traversetest.io — we’ll generate a deletion certificate with timestamps.
What we store, how long, how it's protected.
After source code deletion, one artifact remains: the feature graph.
What’s in the feature graph
- Function/method names and type signatures
- Route definitions (path, HTTP method, middleware chain)
- Database schema (table names, columns, types, FK relationships)
- API endpoints and their signatures
- Call graph (which function calls which)
What’s NOT in it
- Implementation code (the actual code inside functions)
- Secrets, API keys, database passwords
- User data or PII
- Comments, docstrings, env variable values
We scan for PII patterns (SSN, credit card, API key formats) and alert you if found. Pro plan customers can request 7-day retention or immediate deletion.
How we protect it.
Ephemeral containers
Fresh container per test run. Isolated network namespace. No prod access. Destroyed after 5–30 minutes.
AES-256 everywhere
At rest (AES-256-GCM) and in transit (TLS 1.3). Keys in AWS Secrets Manager, separate from data.
Customer-scoped keys
Each account gets its own encryption key. Never shared. Staff cannot decrypt your data.
90-day key rotation
Automated key rotation. Deleted data is cryptographically erased, not just marked for deletion.
Role-based access
RBAC within customer accounts. Granular permissions for test diagnostics, logs, and feature graphs.
Full audit log
Every access event logged and exportable. TraverseTest engineers cannot access data without explicit, logged approval.
Ephemeral databases
Fresh DB per test run with your schema. Reset between tests. Destroyed after completion.
Zero production access
Containers cannot reach your production or staging infrastructure. Network-isolated by design.
Compliance, deployment, and shared responsibility.
Compliance
- SOC 2 Type I completed
- SOC 2 Type II — Q3 2026
- Annual pen test (results under NDA)
- GDPR & CCPA — export/deletion in 30 days
- HIPAA & FedRAMP — not in scope 2026
Infrastructure: US-East AWS. EU residency available (eu-west-1, eu-central-1, eu-north-1).
Deployment
Managed by TraverseTest. US-East or EU.
Your VPC. Zero data egress. Air-gapped supported. See enterprise deployment options.
Self-hosted includes
- Helm charts + Terraform modules
- Air-gapped mode
- SAML/SSO
- Custom retention policies
Shared responsibility
We own
- Secure code handling & deletion
- Ephemeral execution environments
- Encryption at rest & in transit
- Platform access controls & audits
You own
- Org access management
- PR review before merging
- GitHub credential security
- Keeping secrets out of version control
Vulnerability disclosure
security@traversetest.io — 48hr ack, 5-day confirmation, 30-day fix.
Questions? Talk to our security team.
We publish our security posture, share pen test results under NDA, and can join a security review call with your team.